Notify on CloudTrail Event
Overview
The Notify on CloudTrail Event action notifies you of selected CloudTrail events. By integrating this action, you efficiently convert these events into timely insights for quick response and effective management.
This action streamlines the process of staying updated on critical Azure events, ensuring that essential events are promptly received and addressed. It enhances your ability to respond to and manage these events in a timely and organized manner.
Use of this action in a rule
The Notify on CloudTrail Event action must always be used in a rule with the CloudTrail Event trigger, which takes responsibility for sourcing selected events from your CloudTrail logs.
Note: the Run Now button is disabled on any rule that has the Notify on CloudTrail Event action.
Turning events into notifications
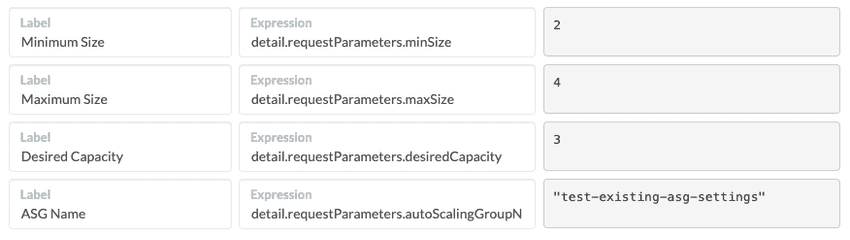
Provide JMESPath expressions to pluck values
from your CloudTrail events. For example, the following expressions pluck key values from
an UpdateAutoScalingGroup event.
Note that for all notifications we automatically include the Account Name, Region, and Event Name values.
Don’t worry about any <no-value> messages that you might see. They just mean that
the sample event currently loaded in the Example Event box in the Notify on CloudTrail Event action
screen does not contain any values that match your JMESPath Expressions. However, you can
replace any <no-value> messages with actual results by pasting an actual event of the
desired type into the Example Box. For example, an UpdateAutoScalingGroup event like
this one was loaded when creating the mappings shown above:
{
"eventInfo": {
"sourceEvent": {
"detail-type": "AWS API Call via CloudTrail",
"source": "aws.autoscaling",
"detail": {
"requestParameters": {
...
"maxSize": 4,
"minSize": 2,
"desiredCapacity": 3,
"autoScalingGroupName": "test-existing-asg-settings",
},
}
},
"source": "aws-cloudwatch"
}
}To find examples of real events that have occurred in your own AWS account, log into CloudTrail in the AWS Console, then click Event History.
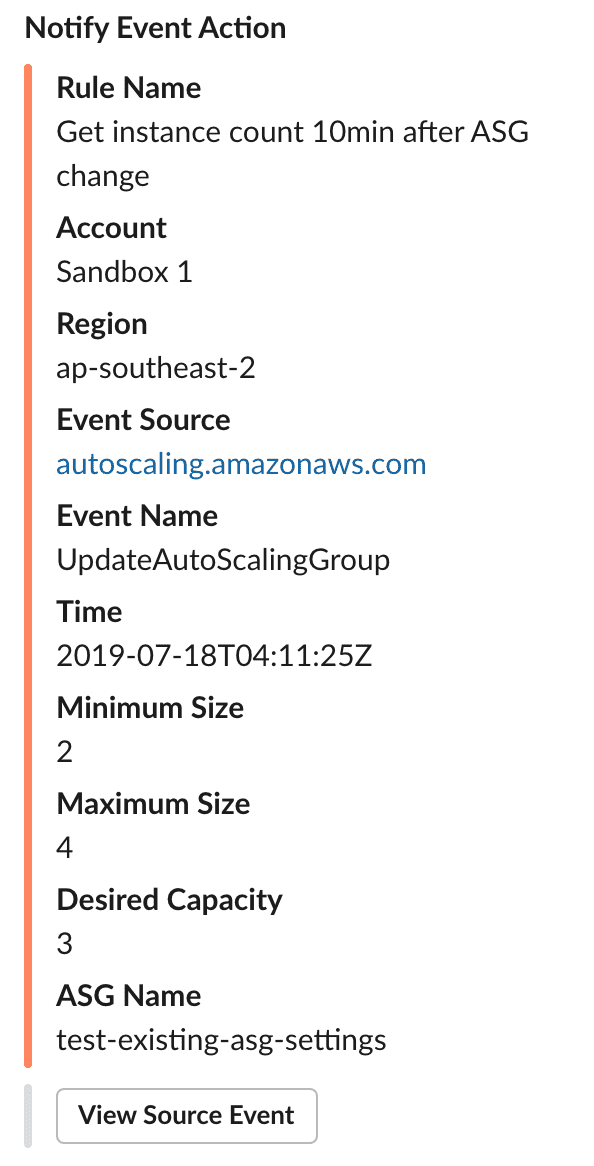
Once you have saved the rule and AWS generates a matching CloudWatch event, you will receive a notification that looks like this: